MFA Is a Strong Lock — But It’s Not the Whole Door
MFA Is a Strong Lock — But It’s Not the Whole Door
Multi-factor authentication (MFA) is a strong front-door lock. But it’s not the only thing that determines whether someone can get in.
Here at AWSMTECH (Switzerland) LTD, we regularly explain to small businesses in Geneva that what happens after login is just as important as the login itself.
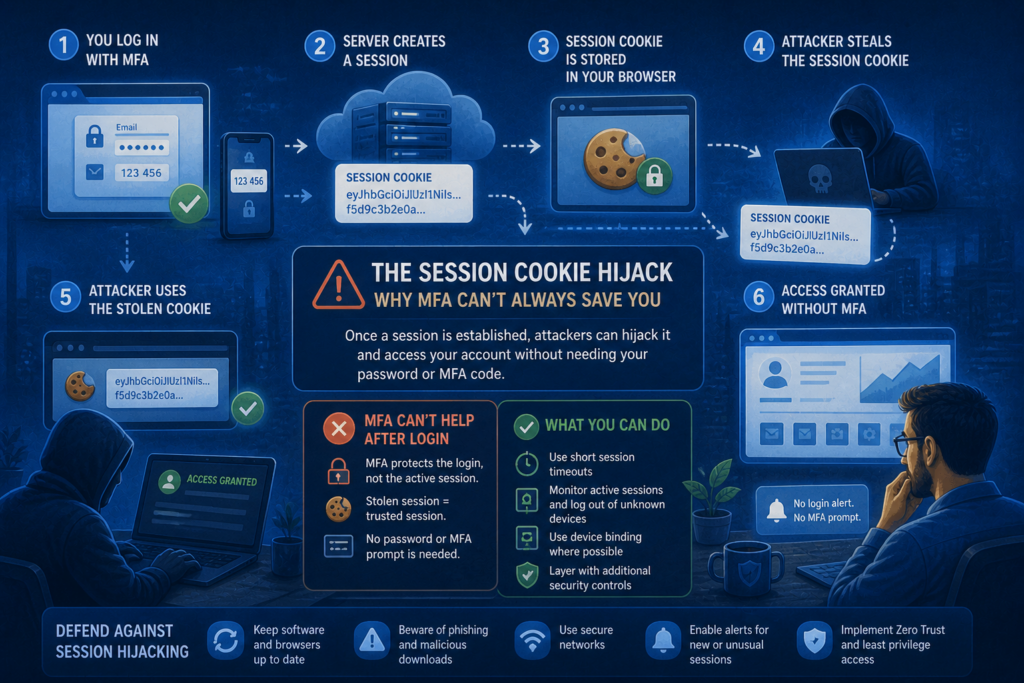
Once you sign in, your browser keeps you authenticated using a session token—often stored as a cookie. Think of it as a wristband at an event. Once security checks you in, the wristband proves you belong. If an attacker steals that wristband, they may not need to challenge MFA at all.
That is the core idea behind session cookie hijacking.
The attacker isn’t breaking MFA. They’re skipping it by replaying your already authenticated session.
This is not a reason to stop using MFA. It’s a reason to stop treating MFA as the finish line.
For businesses across Suisse romande, the practical defence shifts toward layered controls: phishing-resistant authentication, healthy and managed devices, tighter session policies, and monitoring that detects suspicious access early.
Why MFA Isn’t a “Game Over” Control
MFA remains one of the most effective security improvements most organisations can make, and AWSMTECH (Switzerland) LTD strongly recommends it to every client in Geneva. However, MFA alone does not end an attack.
The reason is simple: attackers don’t always try to defeat the login itself. They often go around it.
Cloudflare notes that “attackers are finding new ways to circumvent MFA” and that modern incidents rarely rely on a single technique. Instead, they are part of chained attacks, where one method leads into another.
MFA blocks a large proportion of credential theft. What it does not automatically protect is what happens after a successful sign-in.
That is precisely where session cookie hijacking applies.
Microsoft has described adversary-in-the-middle phishing campaigns in which attackers use reverse-proxy sites to intercept both the user’s credentials and the session cookie that proves an authenticated session exists.
This is not a weakness in MFA. The attacker isn’t defeating MFA—they are reusing the session after MFA has already been completed.
What a Session Cookie Is — and Why Attackers Want It
When you sign in to a web application, the service needs a way to remember that you have already proven your identity. That temporary authenticated state is called a session.
Session identifiers are commonly stored as cookies. Kaspersky explains that session hijacking is often referred to as “cookie hijacking” for exactly this reason.
Attackers target session cookies because they are the shortcut.
Proofpoint describes session tokens as digital “keys” that allow users to stay authenticated. If those keys are stolen, attackers can impersonate legitimate users and potentially bypass authentication controls such as MFA.
That is what makes session cookie hijacking so effective.
If an attacker can capture the cookie representing your active session, they don’t need to break the login process. They simply reuse what you have already completed and gain access to the same applications and data—exactly as if they were sitting at your keyboard.
How Session Cookie Hijacking Actually Happens
Many teams imagine “account takeover” as password guessing or MFA fatigue attacks. Session hijacking works differently.
The attacker’s goal is not to log in as you—it is to take over the proof that you are already logged in and reuse it, often without triggering another authentication challenge.
1) Adversary-in-the-Middle (AiTM) phishing
AiTM phishing is a classic proxy-login trap.
You believe you are signing in to a legitimate site, but instead you are interacting with a look-alike page controlled by the attacker. That page relays the login in real time to the real service, so everything appears normal—including MFA.
Attackers use this technique to intercept the username, password, and session cookie that proves authentication. Again, this is not MFA being broken. MFA succeeds—and the session is stolen immediately afterward.
One known campaign attempted to target more than 10,000 organisations, demonstrating how scalable and effective this technique has become.
2) Browser-in-the-Middle (BitM) session stealing
Browser-in-the-middle attacks take this a step further.
Instead of just proxying the login, the attacker maintains control over the user’s browsing session itself. Google’s threat intelligence team states that stealing a session token is effectively the same as stealing the authenticated session—and once obtained, the attacker no longer needs to perform an MFA challenge.
In this scenario, the attacker is not trying to authenticate instead of the user. They are riding along after authentication has already occurred.
3) Cookie theft from the endpoint
Not all session hijacking involves sophisticated phishing infrastructure.
In some cases, attackers steal session data directly from a compromised device. If malware gains access to an endpoint, it can extract session cookies and reuse them elsewhere.
Session tokens behave like digital keys. If they are taken from an infected device, they can allow attackers to impersonate legitimate users and access sensitive systems without ever touching the login page.
MFA Is a Baseline — Not the Finish Line
MFA remains essential. It blocks a huge category of credential-based attacks and significantly raises the bar for attackers. But session cookie hijacking is a reminder that not every attack focuses on the login step.
For Geneva-based SMEs, the practical response is layered and realistic, not alarmist:
- Make phishing harder through phishing-resistant sign-ins
- Treat device health and patching as part of identity security
- Tighten session behaviour on high-risk applications
- Monitor for suspicious access patterns that indicate session replay
When these controls work together, MFA stops being a comforting checkbox and becomes what it was always meant to be: a strong baseline, supported by protections around the session itself.
Here at AWSMTECH (Switzerland) LTD, we help small and mid-sized businesses across Geneva and Suisse romande design identity protections that reflect how modern attacks actually work.
Contact us today if you would like help protecting your login sessions from hijacking.
